© 2021 Mullins Consulting, Inc. All Rights Reserved Privacy Policy Contact Us


Gaining Knowledge Through Process Mining
by Craig S. Mullins
June 2006

A large wireless phone service provider was concerned with the number of customers it was losing. Every customer lost costs the company $53 in monthly revenue. Although the revenue looks small on a customer by customer basis, with a large customer base the company was losing millions of dollars each month. Using advanced analytics they were able to develop an attrition model to predict which customers were most likely to terminate their contract. In doing so, the company developed a model to cross-
You may not have yet heard the term “process mining” but it is a growing discipline with thriving new technology. Perhaps you have heard of data mining? Process mining is similar. Data mining is an analytical process using heuristics to explore large sets of data in search of consistent patterns and relationships. The goal of data mining is to be able to predict future behavior based on past activity.
Data Mining is an analytic process designed to explore data (usually large amounts of data -
OK, so what does that imply about process mining? Process mining enables the extraction of information from event logs. For example, the audit trails of a workflow management system or the transaction logs of an enterprise resource planning (ERP) system can be used to discover models describing processes, organizations, and products. The information in these logs represents a great wealth of untapped data. Event logs are ubiquitous in transactional information systems (e.g. WFM, ERP, CRM, SCM, and B2B systems) and until recently, the information in these event logs was rarely used to analyze the underlying processes.
So the basic premise behind process mining is to extract details from existing event logs to uncover patterns useful to the business. It is possible to uncover process, control, data, organizational, and social structures from event logs. And perhaps even more importantly, process mining can be used to monitor deviations from normal processing. Such activities are of paramount importance in the day-
To be successful process mining requires so-
There are many potential issues and problems that can be identified and corrected using processing mining. One such byproduct of process mining is simply identifying that critical activities are occurring as needed and when required. Additional solutions that can be arrived at using process mining include characterizing failures and successes. After finding the factors that lead to success steps can then be taken to optimize the workflow for future successes. When there are multiple choices within a workflow process mining can analyze the past choices to determine which more often led to desired results.
Process mining also can assist with general optimization. For example, process mining can help to identify redundant activities and operations which require restructuring. Moreover, process mining can be used to identify deviations from some desired process, e.g., some reference model or set of guidelines.
Example Applications
As we’ve established, the goal of process mining is to extract information about processes from transaction logs. Transaction logs hold a wealth of information across multiple types of applications, of which we will explore several examples. For process mining to be effective the information captured on the transaction logs must be of the following makeup:
- each event refers to an activity (that is, a well-
defined step in the process), - each event refers to a case (that is, a process instance),
- each event can have a performer also referred to as originator (the person executing or initiating the activity), and
- events have a timestamp and are totally ordered.
In addition events may have associated data (e.g., the outcome of a decision). Events are recorded in a so-
Case ID Activity ID Originator Timestamp
case 1 activity A Joe 2005-
case 2 activity A Joe 2005-
case 3 activity A Elizabeth 2005-
case 3 activity D Carol 2005-
case 1 activity B Mike 2005-
…and so on
This information can be used to extract knowledge. Many applications and systems produce transaction logs similar in nature to this.
Process mining is particularly useful in situations where events are recorded but there is no system enforcing people to work in a particular way. Consider for example a hospital where the diagnosis and treatment activities are recorded in the hospital information system, but where health-
A more common example is provided by an e-
It is also possible to construct social networks from e-
The challenge of process mining is to identify the case and the task for each event that is recorded. For example, given an e-
Enterprise resource planning applications such as SAP R/3 and Peoplesoft are also rich sources of process information that can be mined. However, the task of process mining such applications can be problematic.
SAP R/3, for example, creates many logs and reports. Unfortunately, the logs are either at a very detailed level or very specific for a given process. For example, reports such as the ST03 Transaction Report can be used to inspect database transactions. But these transactions are too fine-
ProM: A Framework for Process Mining
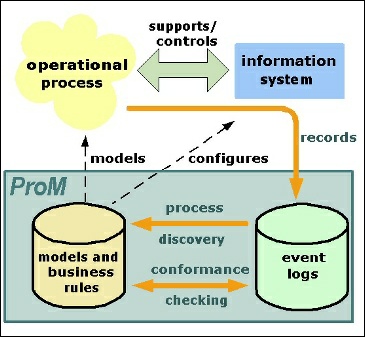
One example of a process mining implementation is the ProM (Process Mining) framework developed at Eindhoven University of Technology. The ProM framework provides a wide range of process miming techniques.
ProM has been developed as a platform for process mining algorithms and tools. Process mining aims at extracting information from event logs to capture the business process as it is being executed. Refer to Figure 1 for clarification. It provides an overview of process mining and the various relations between entities such as the information system, operational process, event logs and process models.
 According to Wil van der Aalst, full professor at the Information Systems department of the Faculty of Technology Management of Eindhoven University of Technology, his team has used the ProM framework to mine several processes in practice, and have recently begun to mine hospital processes.
According to Wil van der Aalst, full professor at the Information Systems department of the Faculty of Technology Management of Eindhoven University of Technology, his team has used the ProM framework to mine several processes in practice, and have recently begun to mine hospital processes.
The original purpose for the ProM framework was to serve as a platform for process mining. As development ensued the scope of the framework grew broader to encompass tasks ranging from process verification to social network analysis to conformance checking and more. Additionally, the ProM framework supports a wide variety of process models enabling plug-
For example, people can take transaction log from, say, IBM's WebSphere, transform it to MXML using ProM import, discover a process model in terms of a heuristics net, and convert the heuristics net to a Petri net for analysis. Such application scenarios are supported by ProM and demonstrate true model interoperability.
With respect to the applications discussed in the previous section, ProM can be deployed against Microsoft Outlook e-
Professor van der Aalst notes that several techniques have been deployed to overcome these problems, including the use of genetic algorithms that are robust to noise. The professor goes on to say that “experiments show that the fitness measure leads to the mining of process models that can reproduce all the behavior in the log, but these mined models may also allow for extra behavior. In short, the current version of the genetic algorithm can already be used to mine process models, but future research is necessary to always ensure that the mined models do not allow for extra behavior.”
Bottom Line
The basic idea of process mining is to extract knowledge from event logs recorded by an information system. Using process mining techniques, the rich data resources just lying around in the transaction and workflow logs of popular application software can be turned into vital knowledge about your business operations. A thorough analysis of this information can greatly improve your business processes.
Enterprise
Leadership
Figure 1. The ProM Framework
From Enterprise Leadership, June 2006.
© 2012 Craig S. Mullins,
